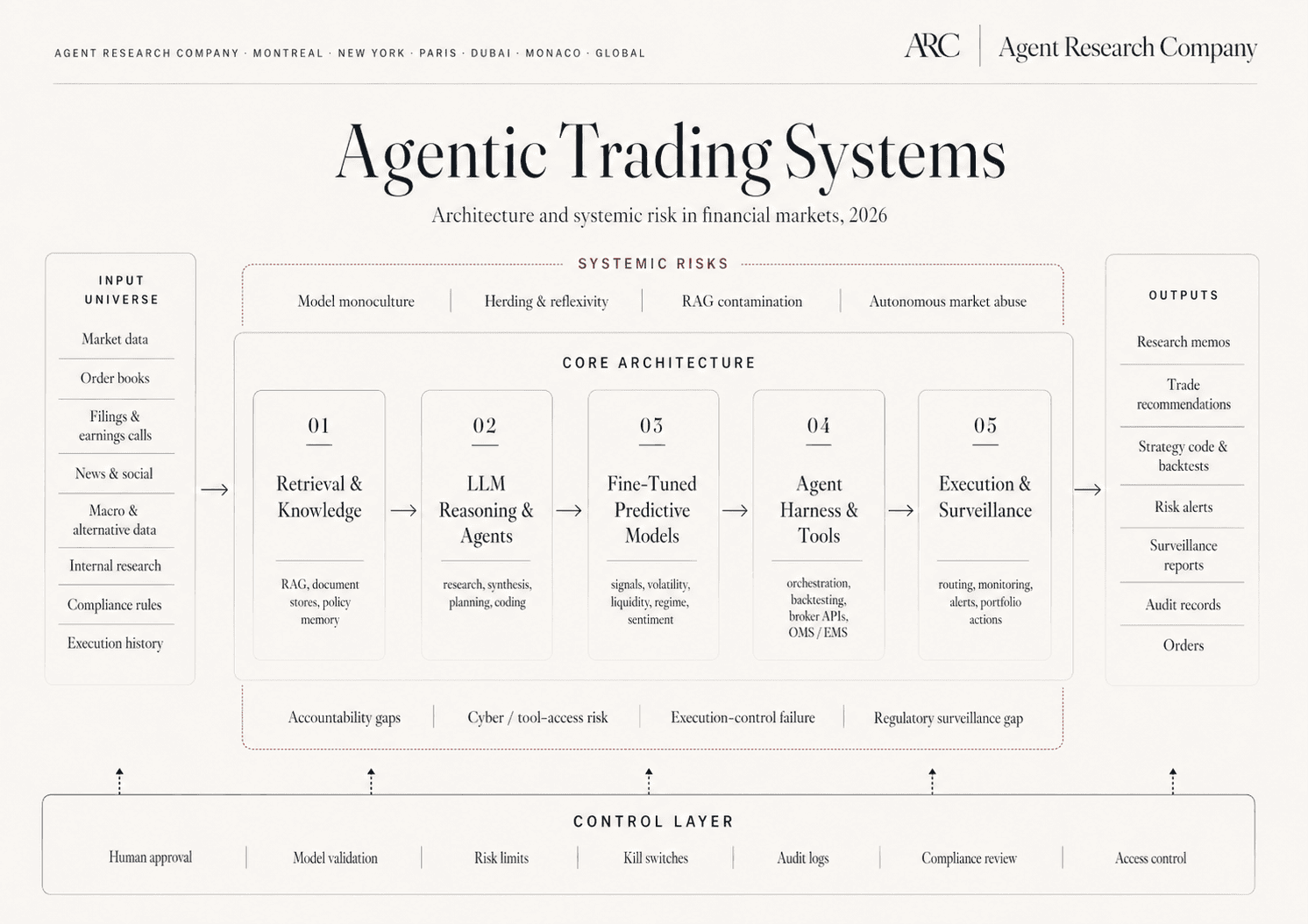
The agentic hedge fund is no longer a thought experiment. Multi-strategy funds are operating with single analyst desks supervising fleets of agents that perform research, risk, and execution work that previously required hundreds of headcount. At least one well-known fund operates with no human analysts at all. The architectural pattern is consistent: a small number of named agent roles, mapped one-to-one onto the named functions of a traditional investment firm, with hard supervisory boundaries between layers.
This page describes that pattern as an engagement. It is a written, named build of the role topology, the authorization granularity between agents, the decision-log schema, and the supervisory artifacts that an institutional proxy will be evaluated against in the next 12–24 months. It is the engagement most useful to firms that have decided to build but have not yet committed architecturally.